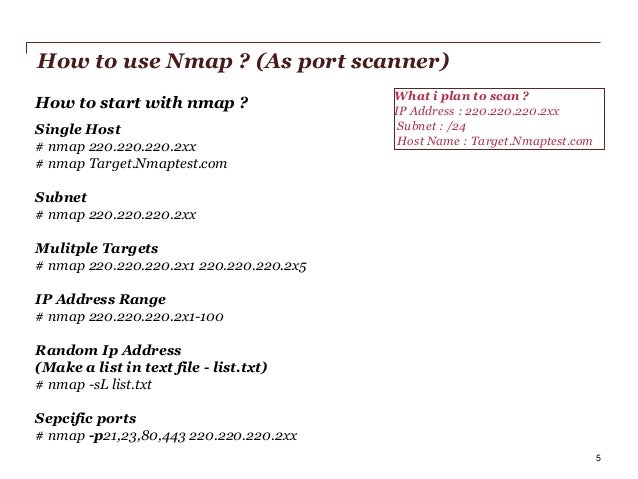
Fig.01: nmap output #2: Scan multiple IP address or subnet (IPv4) nmap 192.168.1.1 192.168.1.2 192.168.1.3 ## works with same subnet i.e. 192.168.1.0/24 nmap 192.168.1.1,2,3 You can scan a range of IP addresses too: nmap 192.168.1.1-20 You can scan a range of IP address using a wildcard: nmap 192.168.1.
Finally, you scan an entire subnet: nmap 192.168.1.0/24 #3: Read list of hosts/networks from a file (IPv4) The -iL option allows you to read the list of target systems using a text file. This is useful to scan a large number of hosts/networks. Nmap -p port hostName ## Scan port 80 nmap -p 80 192.168.1.1 ## Scan TCP port 80 nmap -p T: 80 192.168.1.1 ## Scan UDP port 53 nmap -p U: 53 192.168.1.1 ## Scan two ports ## nmap -p 80, 443 192.168.1.1 ## Scan port ranges ## nmap -p 80- 200 192.168.1.1 ## Combine all options ## nmap -p U: 53, 111, 137,T: 21- 25, 80, 139, 8080 192.168.1.1 nmap -p U: 53, 111, 137,T: 21- 25, 80, 139, 8080 server1.cyberciti.biz nmap -v -sU -sT -p U: 53, 111, 137,T: 21- 25, 80, 139, 8080 192.168.1.254 ## Scan all ports with. wildcard ## nmap -p '.' 192.168.1.1 ## Scan top ports i.e.
Use Nmap To Quickly Scan A Large Subnet For Mac
Scan $number most common ports ## nmap -top-ports 5 192.168.1.1 nmap -top-ports 10 192.168.1.1 Sample outputs. Starting Nmap 5.00 ( ) at 2012- 11- 27 01: 23 IST Interesting ports on 192.168.1.1: PORT STATE SERVICE 21/tcp closed ftp 22/tcp open ssh 23/tcp closed telnet 25/tcp closed smtp 80/tcp open http 110/tcp closed pop3 139/tcp closed netbios-ssn 443/tcp closed https 445/tcp closed microsoft-ds 3389/tcp closed ms-term-serv MAC Address: BC:AE:C5:C3: 16: 93 (Unknown ) Nmap done: 1 IP address ( 1 host up ) scanned in 0.51 seconds #16: The fastest way to scan all your devices/computers for open ports ever nmap -T5 192.168.1.0/24 #17: How do I detect remote operating system? Nmap -O 192.168.1.1 nmap -O -osscan-guess 192.168.1.1 nmap -v -O -osscan-guess 192.168.1.1 Sample outputs: Starting Nmap 5.00 ( ) at 2012-11-27 01:29 IST NSE: Loaded 0 scripts for scanning.
Initiating ARP Ping Scan at 01:29 Scanning 192.168.1.1 1 port Completed ARP Ping Scan at 01:29, 0.01s elapsed (1 total hosts) Initiating Parallel DNS resolution of 1 host. At 01:29 Completed Parallel DNS resolution of 1 host.
At 01:29, 0.22s elapsed Initiating SYN Stealth Scan at 01:29 Scanning 192.168.1.1 1000 ports Discovered open port 80/tcp on 192.168.1.1 Discovered open port 22/tcp on 192.168.1.1 Completed SYN Stealth Scan at 01:29, 0.16s elapsed (1000 total ports) Initiating OS detection (try #1) against 192.168.1.1 Retrying OS detection (try #2) against 192.168.1.1 Retrying OS detection (try #3) against 192.168.1.1 Retrying OS detection (try #4) against 192.168.1.1 Retrying OS detection (try #5) against 192.168.1.1 Host 192.168.1.1 is up (0.00049s latency). ### Stealthy scan ### nmap -sS 192.168.1.1 ### Find out the most commonly used TCP ports using TCP connect scan (warning: no stealth scan) ### OS Fingerprinting ### nmap -sT 192.168.1.1 ### Find out the most commonly used TCP ports using TCP ACK scan nmap -sA 192.168.1.1 ### Find out the most commonly used TCP ports using TCP Window scan nmap -sW 192.168.1.1 ### Find out the most commonly used TCP ports using TCP Maimon scan nmap -sM 192.168.1.1 #23: Scan a host for UDP services (UDP scan) Most popular services on the Internet run over the TCP protocol. DNS, SNMP and DHCP are three of the most common UDP services. Use the following syntax to find out UDP services: nmap -sU nas03 nmap -sU 192.168.1.1 Sample outputs. ## TCP Null Scan to fool a firewall to generate a response ## ## Does not set any bits (TCP flag header is 0) ## nmap -sN 192.168.1.254 ## TCP Fin scan to check firewall ## ## Sets just the TCP FIN bit ## nmap -sF 192.168.1.254 ## TCP Xmas scan to check firewall ## ## Sets the FIN, PSH, and URG flags, lighting the packet up like a Christmas tree ## nmap -sX 192.168.1.254 See with iptables. #26: Scan a firewall for packets fragments The -f option causes the requested scan (including ping scans) to use tiny fragmented IP packets. The idea is to split up the TCP header over several packets to make it harder for packet filters, intrusion detection systems and other annoyances to detect what you’re doing.
Nmap -f 192.168.1.1 nmap -f fw2.nixcraft.net.in nmap -f 15 fw2.nixcraft.net.in ## Set your own offset size with the -mtu option ## nmap -mtu 32 192.168.1.1 #27: Cloak a scan with decoys The -D option it appear to the remote host that the host(s) you specify as. Thus, their IDS might report 5-10 port scans from unique IP addresses, but they won’t know which IP was scanning them and which were innocent decoys: nmap -n -Ddecoy-ip1,decoy-ip2,your-own-ip,decoy-ip3,decoy-ip4 remote-host-ip nmap -n -D192.168.1.5,10.5.1.2,172.1.2.4,3.4.2.1 192.168.1.5 #28: Scan a firewall for MAC address spoofing. ### Spoof your MAC address ## nmap -spoof-mac MAC-ADDRESS-HERE 192.168.1.1 ### Add other options ### nmap -v -sT -PN -spoof-mac MAC-ADDRESS-HERE 192.168.1.1 ### Use a random MAC address ### ### The number 0, means nmap chooses a completely random MAC address ### nmap -v -sT -PN -spoof-mac 0 192.168.1.1 #29: How do I save output to a text file? The syntax is: nmap 192.168.1.1 output.txt nmap -oN /path/to/filename 192.168.1.1 nmap -oN output.txt 192.168.1.1 BONUS – #30: Not a fan of command line tools?
Try front end: Zenmap is the official Nmap Security Scanner GUI. It is a multi-platform (Linux, Windows, Mac OS X, BSD, etc.) free and open source application which aims to make Nmap easy for beginners to use while providing advanced features for experienced Nmap users. Frequently used scans can be saved as profiles to make them easy to run repeatedly. A command creator allows interactive creation of Nmap command lines.

Scan results can be saved and viewed later. Saved scan results can be compared with one another to see how they differ. The results of recent scans are stored in a searchable database. You can install zenmap using the following: $ sudo apt-get install zenmap Sample outputs: sudo password for vivek: Reading package lists. Done Building dependency tree Reading state information. Done The following NEW packages will be installed: zenmap 0 upgraded, 1 newly installed, 0 to remove and 11 not upgraded. Need to get 616 kB of archives.
After this operation, 1,827 kB of additional disk space will be used. Get:1 squeeze/main zenmap amd64 5.00-3 616 kB Fetched 616 kB in 3s (199 kB/s) Selecting previously deselected package zenmap. (Reading database. 281105 files and directories currently installed.) Unpacking zenmap (from./zenmap5.00-3amd64.deb). Processing triggers for desktop-file-utils.
Processing triggers for gnome-menus. Processing triggers for man-db. Setting up zenmap (5.00-3). Processing triggers for python-central. Type the following command to start zenmap: $ sudo zenmap Sample outputs.